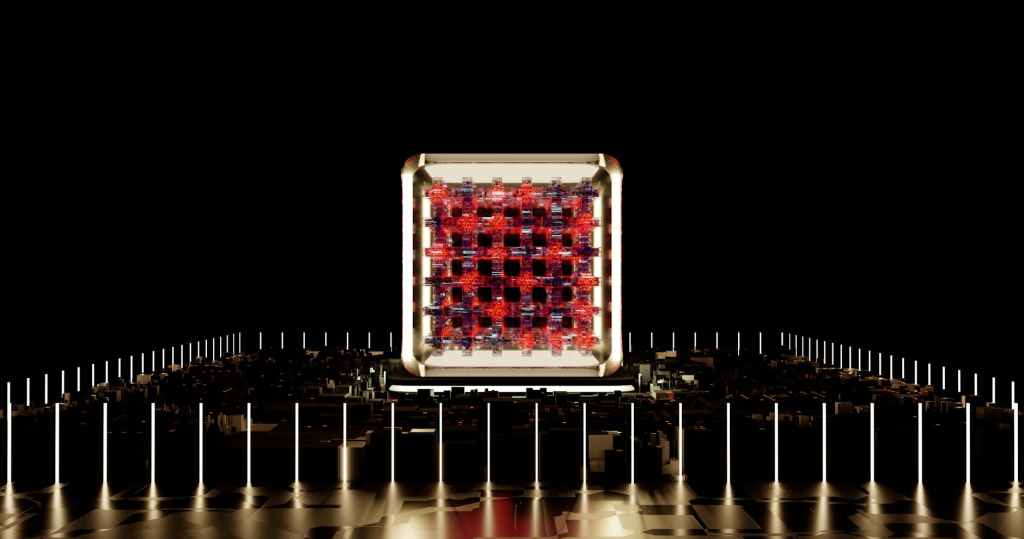
Quantum computers, machines that harness the strange rules of quantum physics, are poised to reshape industries ranging from pharmaceuticals to national security. Though still in early stages of development, these devices operate fundamentally differently from today’s digital computers by using quantum bits, or qubits, which can exist in multiple states at once and become entangled with one another. This opens the door to computing capabilities that far exceed what classical systems can achieve in specific tasks.
Advertisement

Is artificial intelligence tracking you? This clothing line is designed to confuse AI. Click here to learn more.
Rather than replacing conventional computers, quantum systems are expected to work alongside them, accelerating solutions to problems that are currently intractable. Researchers envision applications including molecular simulation for drug discovery, optimization of complex industrial processes, and decryption of data that is currently considered secure. Despite the hype, most practical uses remain years or decades away. Still, recent studies have demonstrated early signs of what scientists call “quantum advantage” — instances where quantum processors outperform their classical counterparts on certain tests.
The underlying principles of quantum computing rely on phenomena such as superposition — where particles can exist in multiple states at once — and entanglement, which allows particles to be instantaneously linked across distances. These properties allow quantum computers to explore a vast number of possibilities simultaneously, offering potential breakthroughs in areas like materials science and logistics. However, limitations on how much data can be extracted from a quantum system after processing remain a significant technical hurdle.
Advertisement
Have you or a loved one ever consumed CAFFEINE? You may be eligible to purchase a coffee mug. Click here to learn more.
The idea of quantum computing has existed since the 1980s, with physicists like Richard Feynman proposing its use to simulate physical systems more efficiently. In the 1990s, the theoretical groundwork expanded when Peter Shor introduced a quantum algorithm capable of breaking widely used encryption techniques, highlighting the geopolitical and security implications of the technology. Since then, progress has been steady, if slow. Several early demonstrations have shown promise, though none have yet yielded transformative results.
Currently, quantum computers are constrained by the fragility of qubits, which can easily lose their quantum state due to environmental interference such as temperature fluctuations or radiation. The most advanced machines today use a few hundred qubits but still suffer from frequent errors. Research labs and tech companies are exploring a variety of qubit technologies, from trapped ions and superconducting circuits to more experimental designs like topological qubits, in an effort to improve performance and stability.
Looking forward, experts anticipate that quantum computers will not become everyday consumer devices but will be housed in specialized facilities. These systems will serve as powerful tools for scientific research, industry innovation, and secure communication networks. Meanwhile, agencies like the National Institute of Standards and Technology (NIST) are already preparing for a future where quantum computers could pose a threat to current encryption by developing quantum-resistant cryptographic standards.
Article by multiple RFHC contributors, based upon information from a press release by the National Institute of Standards and Technology (NIST)
Advertisement

Is artificial intelligence tracking you? This clothing line is designed to confuse AI. Click here to learn more.